,I am Sashwat.
I build products, Linux automation, and confidential computing tooling end-to-end — taking them from a blank page to running in production. I am currently open to open source, consulting, and full-time roles.

Building Confidential Computing Products at IBM on LinuxONE.
Years building things end-to-end
From embedded systems to enterprise cloud, I've designed and shipped full-stack products across multiple domains.
Years in enterprise engineering
Scaling Linux infrastructure and confidential computing platforms at IBM, AMD, and Xilinx.
Open source projects in production
Go SDKs, Terraform providers, and embedded tooling built in the open and used by enterprise teams.
More than shipping code — I build products and the systems they run on.
From Confidential Computing at IBM to silicon-level DevOps at AMD–Xilinx — I own the full build, from requirements to a deploy that survives real traffic.
What I’m working on
From enterprise to side projects.
IBM Confidential Computing by day — OS, Go SDKs, Terraform providers, and CLIs used by enterprise teams. IoT, hardware, and apps by night.
- IBM · Public
ibm-hyper-protect/contract-go
Go SDK for generating confidential workload contracts — signing, attestation, and encryption end-to-end.
- IBM · Public
ibm-hyper-protect/terraform-provider-hpcr
Declarative contract generation for IBM Confidential Computing Container Runtime.
- Personal
sashuu69/iot-water-level-indicator
IoT-based water level indicator — Raspberry Pi, Arduino, Firebase, and an Android app.
- Personal
sashuu69/portfolio-website-infrastructure
Terraform and Ansible code to self-host a portfolio website on AWS with automated SSL.
Selected work
Things I’ve shipped end-to-end.
From the build
Recent writing.
Field notes from production — backend systems, Linux automation, and the seams where they meet.

Building the IBM Confidential Computing Contract Toolchain
Why we built contract-go, contract-cli, and a Terraform provider to ship confidential workloads on IBM Confidential Computing without hand-rolling crypto.
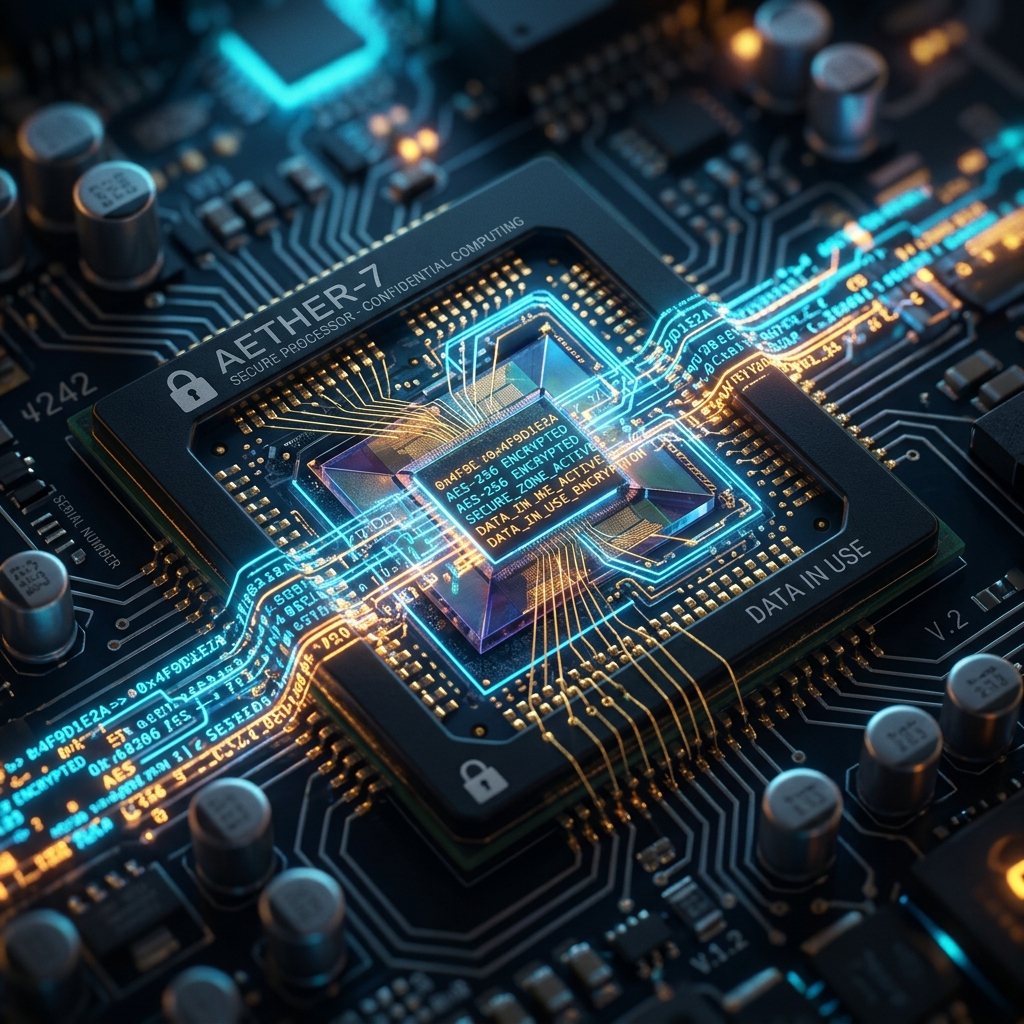
Confidential Computing: Securing Data During Processing
Why encryption at rest and in transit aren't enough, what trusted execution environments add, and where confidential computing fits.

